Introducing the Paraxial.io GitHub App
Michael Lubas, 2024-01-03
Modern software development means code changes are pushed into production on a daily basis. A traditional penetration testing engagement provides a snapshot of an application’s security. True security requires automation, where every new change is analyzed.
Elixir has excellent open source security tools, including Sobelow for code security. Why is Paraxial.io needed? Consider the following Sobelow findings:
Config.CSRFRoute: CSRF via Action Reuse
Misc.BinToTerm: Unsafe `binary_to_term`
Config.CSP: Missing Content-Security-Policy
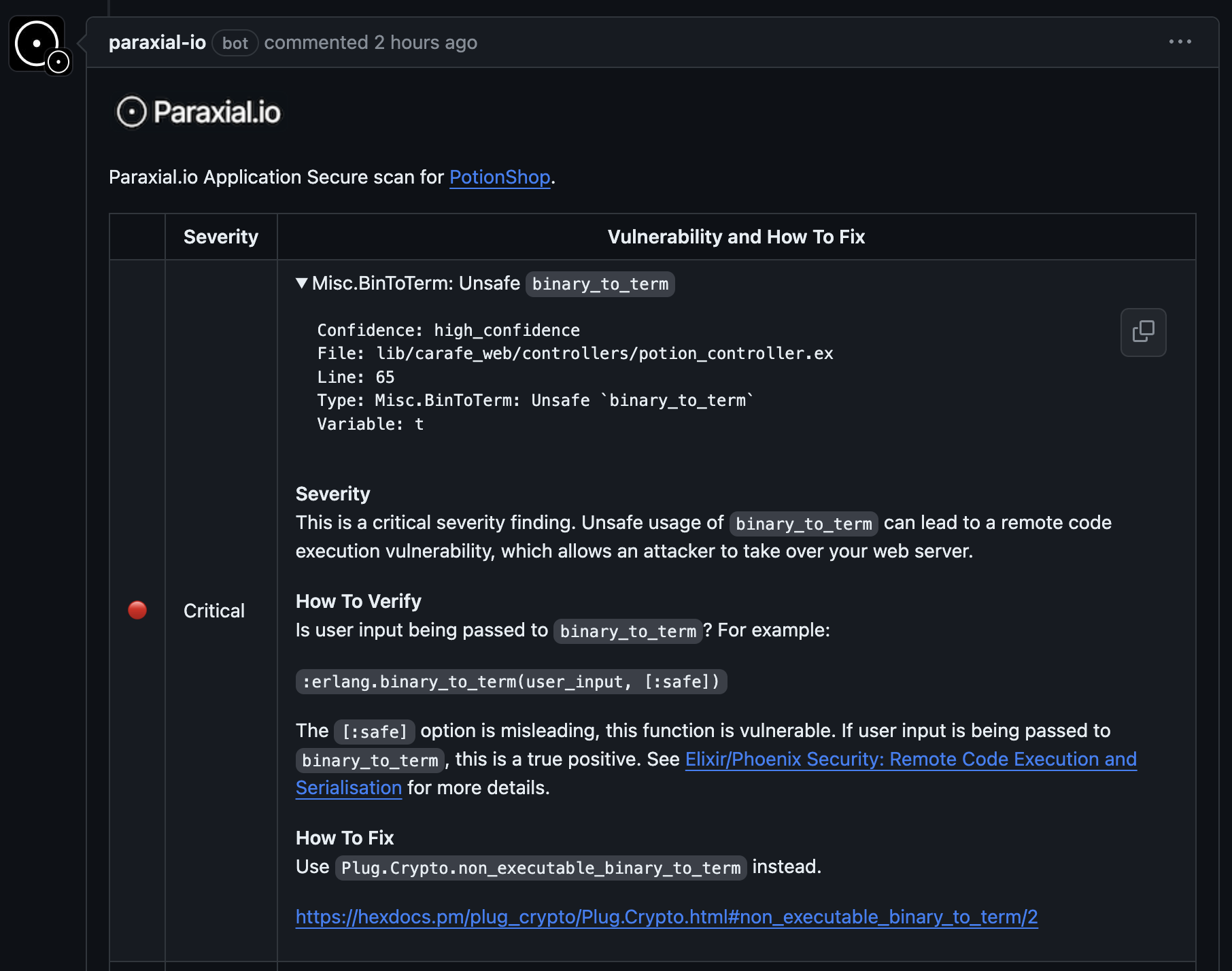
How would you rank these by priority? How do you fix each one? The task of triaging and remediating findings can be frustrating, leading some teams to ignore them completely. Paraxial.io is able to prioritize these findings, highlighting the fact that BinToTerm is the worst one.
Today the Paraxial.io GitHub App is live, providing actionable security feedback to developers, right in the pull request:
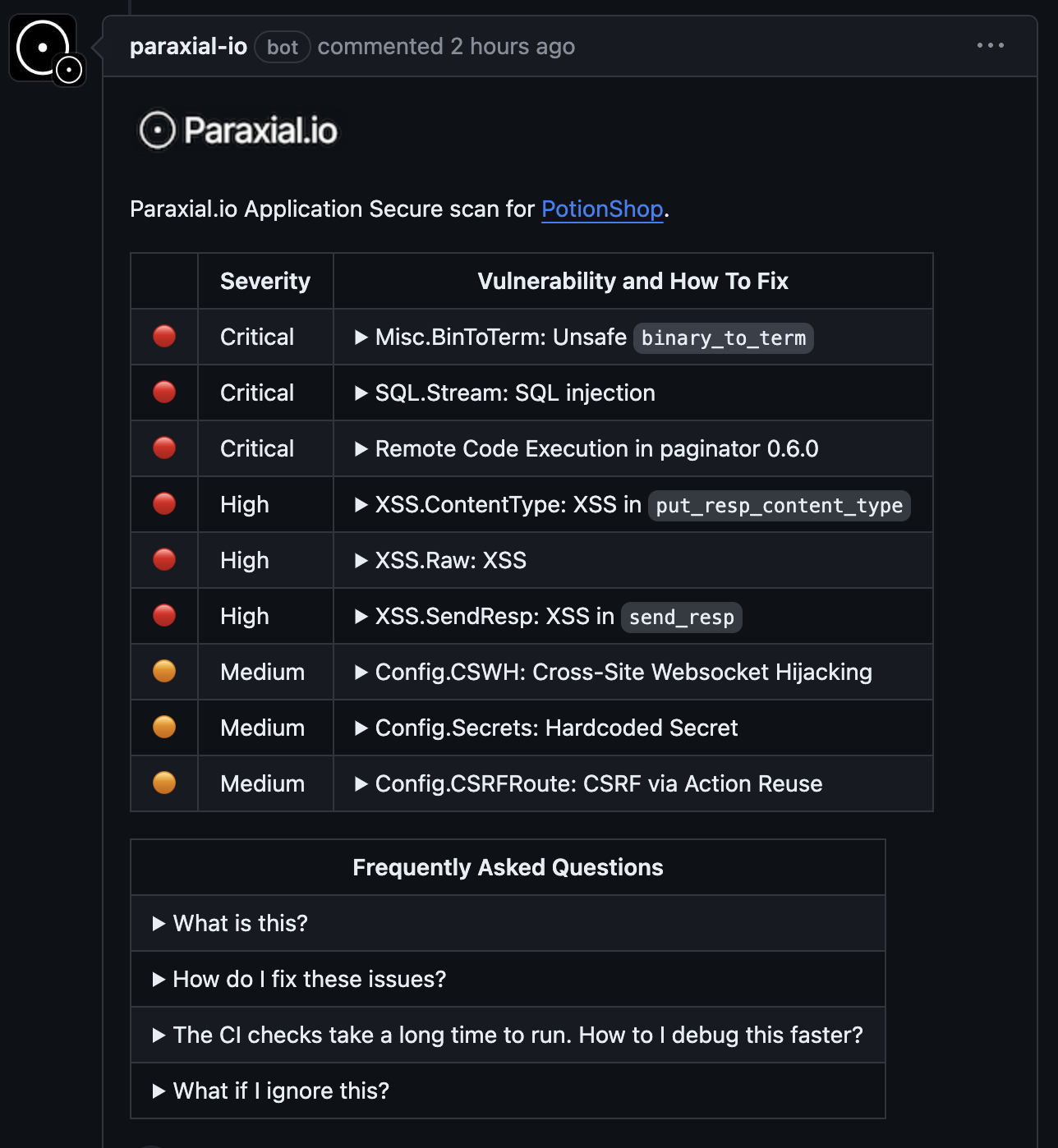
Each finding includes detailed information on vulnerability impact and how to resolve it.
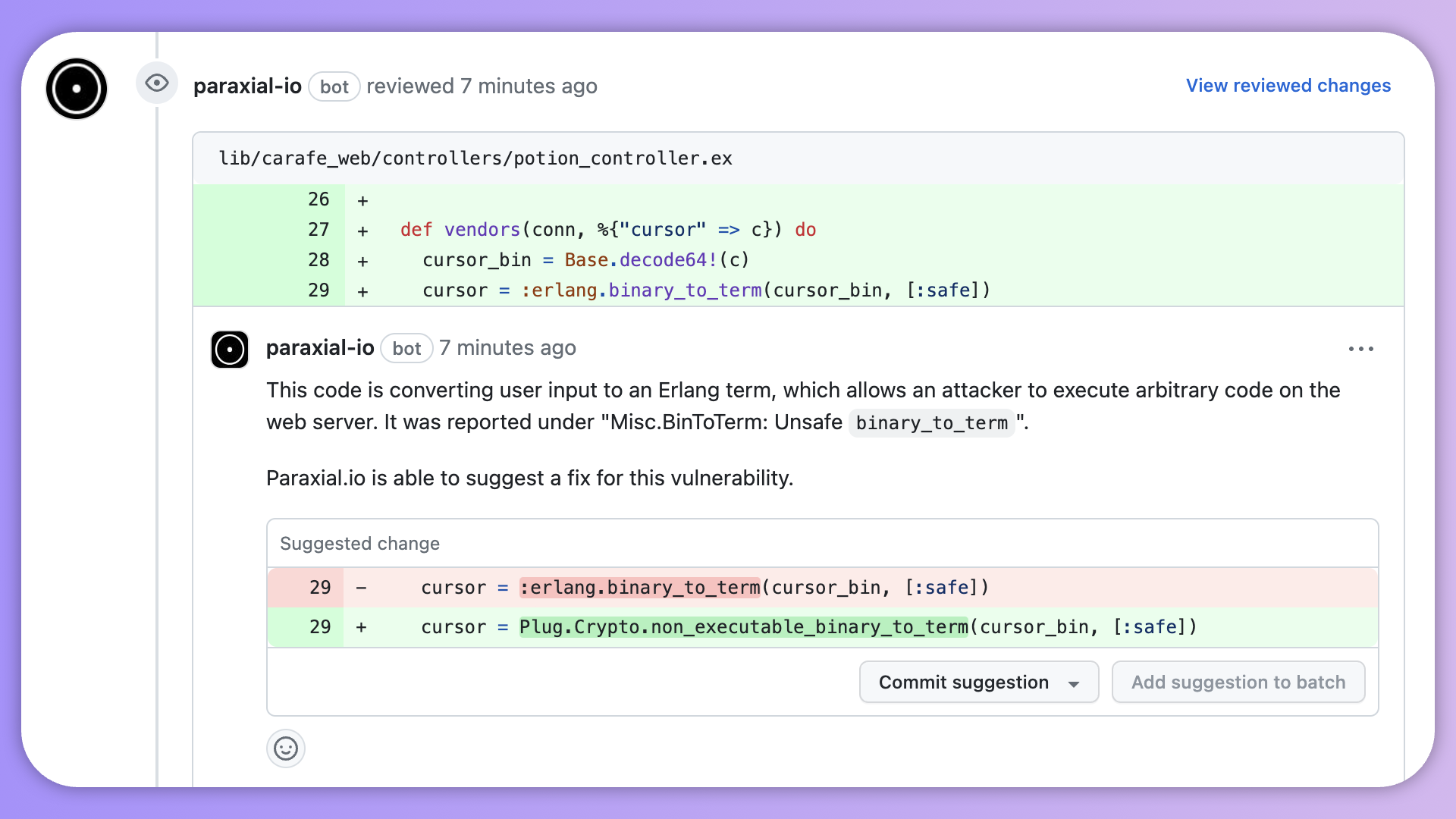
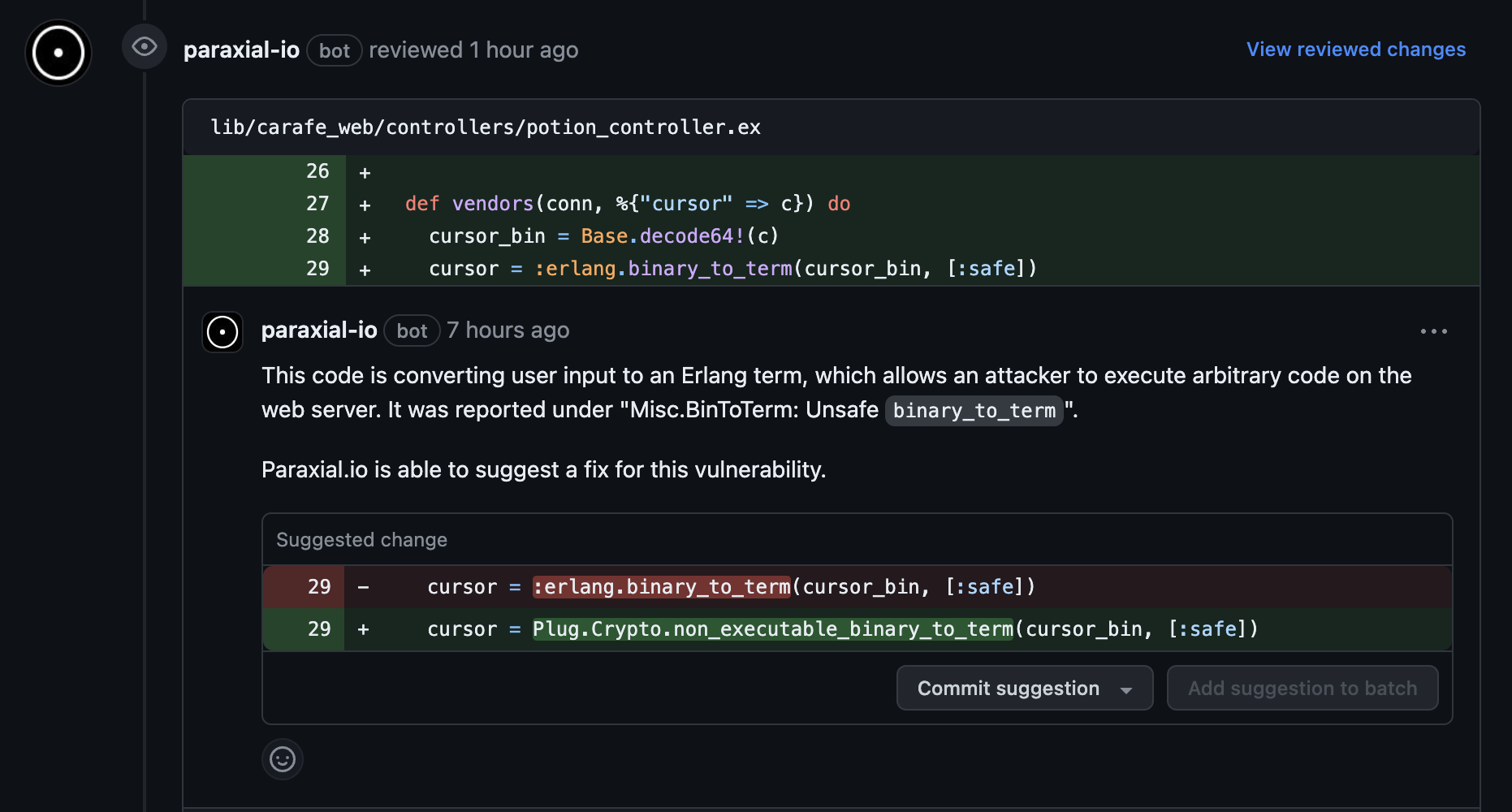
In some cases, Paraxial.io can even suggest a fix.
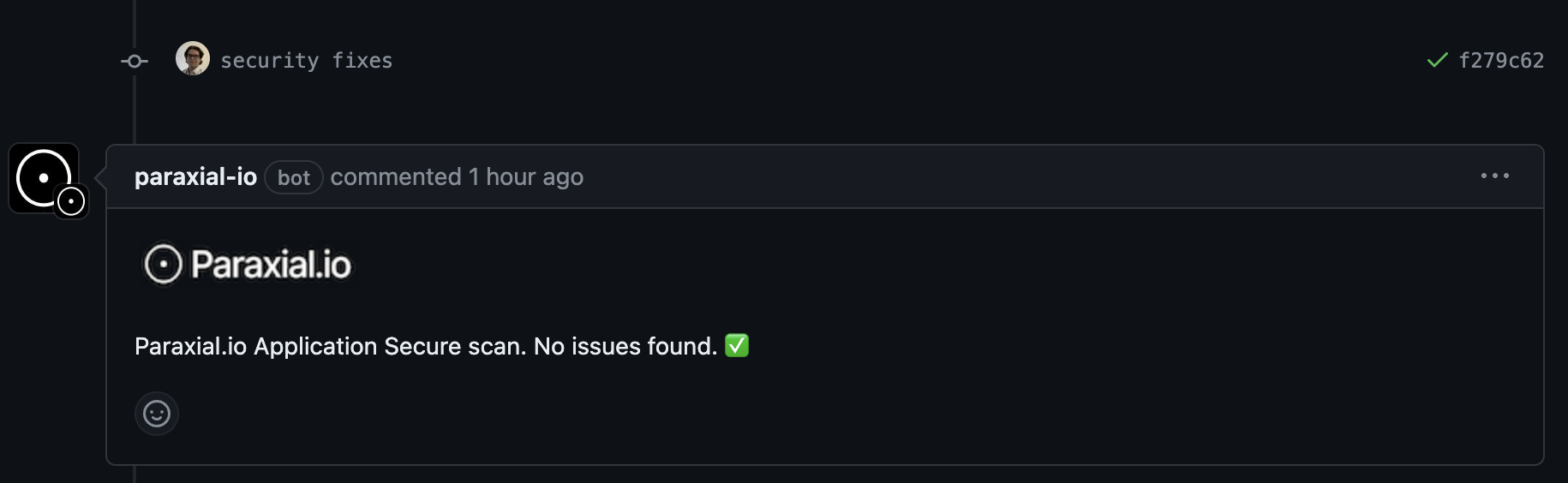
When the issues are fixed, Paraxial.io will report this in the PR and keep a record for future compliance audits.
If you are currently a Paraxial.io customer, see the documentation page for setup instructions. If you would like to start using Paraxial.io, please reach out today.
Paraxial.io stops data breaches by helping developers ship secure applications. Get a demo or start for free.