Introducing Paraxial.io 2.0
Michael Lubas, 2023-12-06
Today Paraxial.io 2.0 is live, delivering major improvements to help you secure your Elixir and Phoenix applications. How many internet facing Elixir apps do you currently have? When was the last time each one received a security scan? How many critical and high vulnerabilities are outstanding? Paraxial.io makes the complex task of understanding your security posture simple.
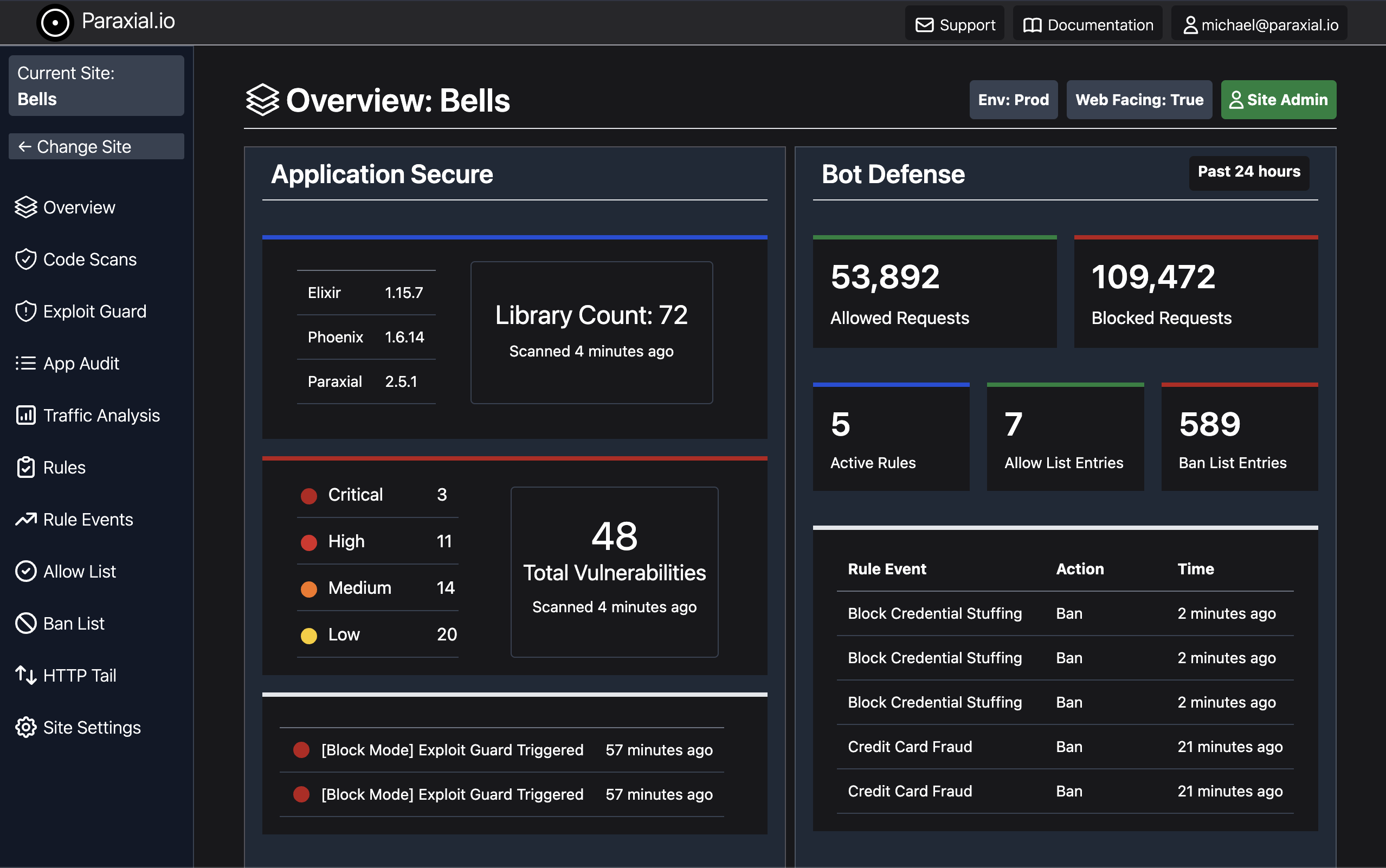
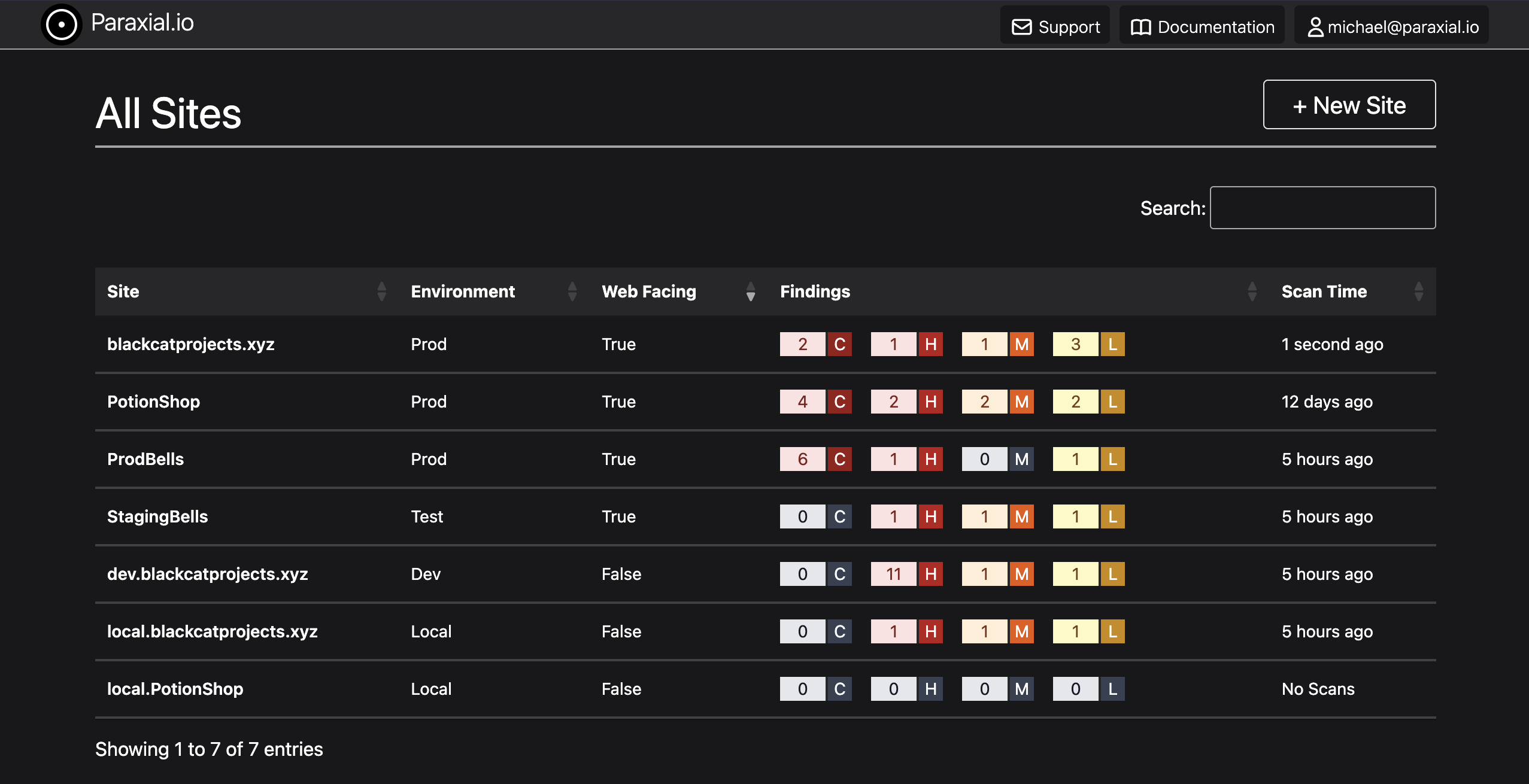
Asset Management
Security starts with understanding your network better than attackers do. The newly revamped Sites page displays all of your Elixir applications, with information on deployment environments, internet exposure status, and a summary of active vulnerabilities.
Overview
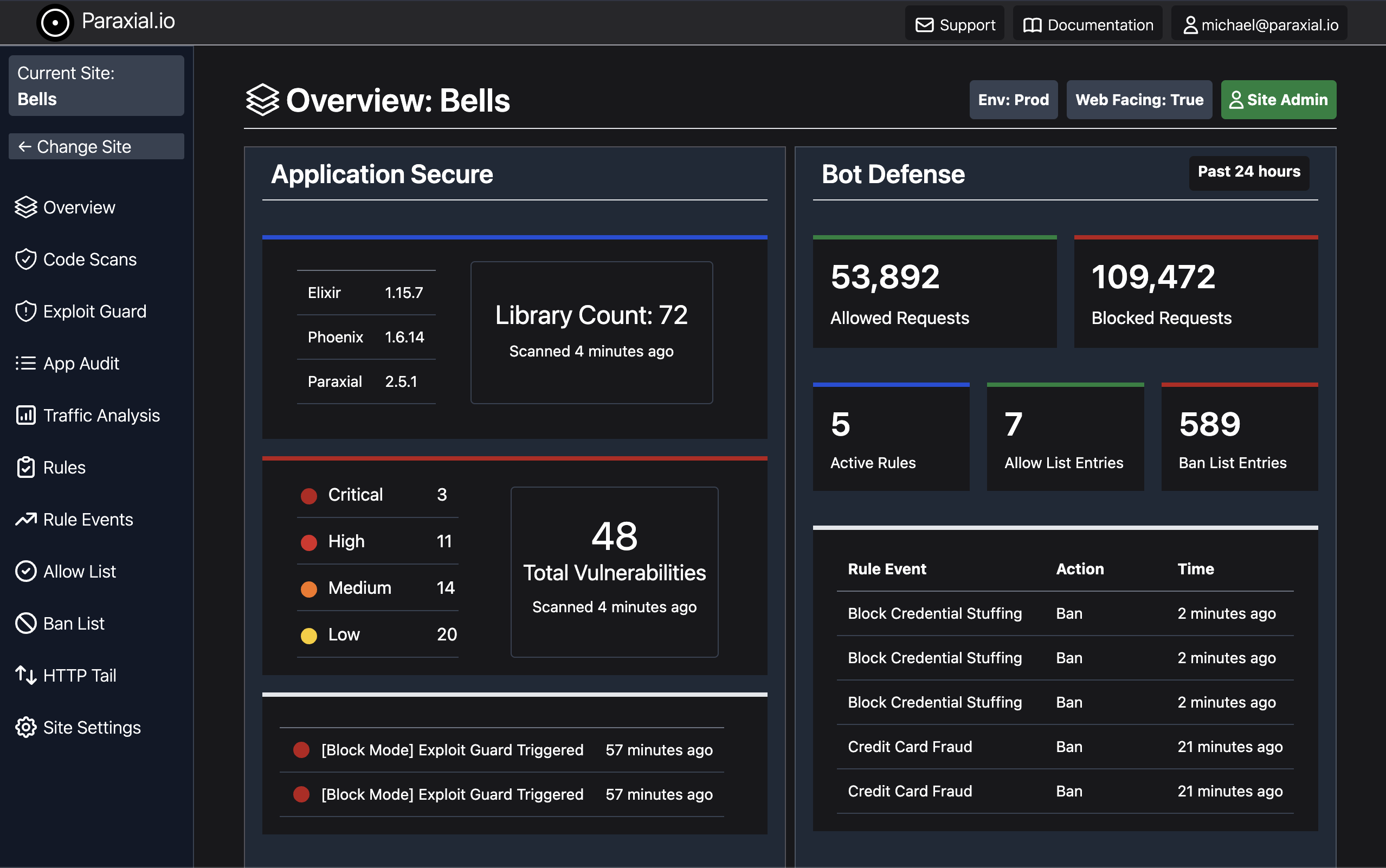
There are a number of security metrics relevant to Elixir applications, including:
- Active vulnerabilities
- Dependency versions
- Recent exploitation attempts
- HTTP traffic
- Rules for restricting bot attacks
The new Overview page for each site displays the most relevant information on one screen, saving your team time and improving your security posture.
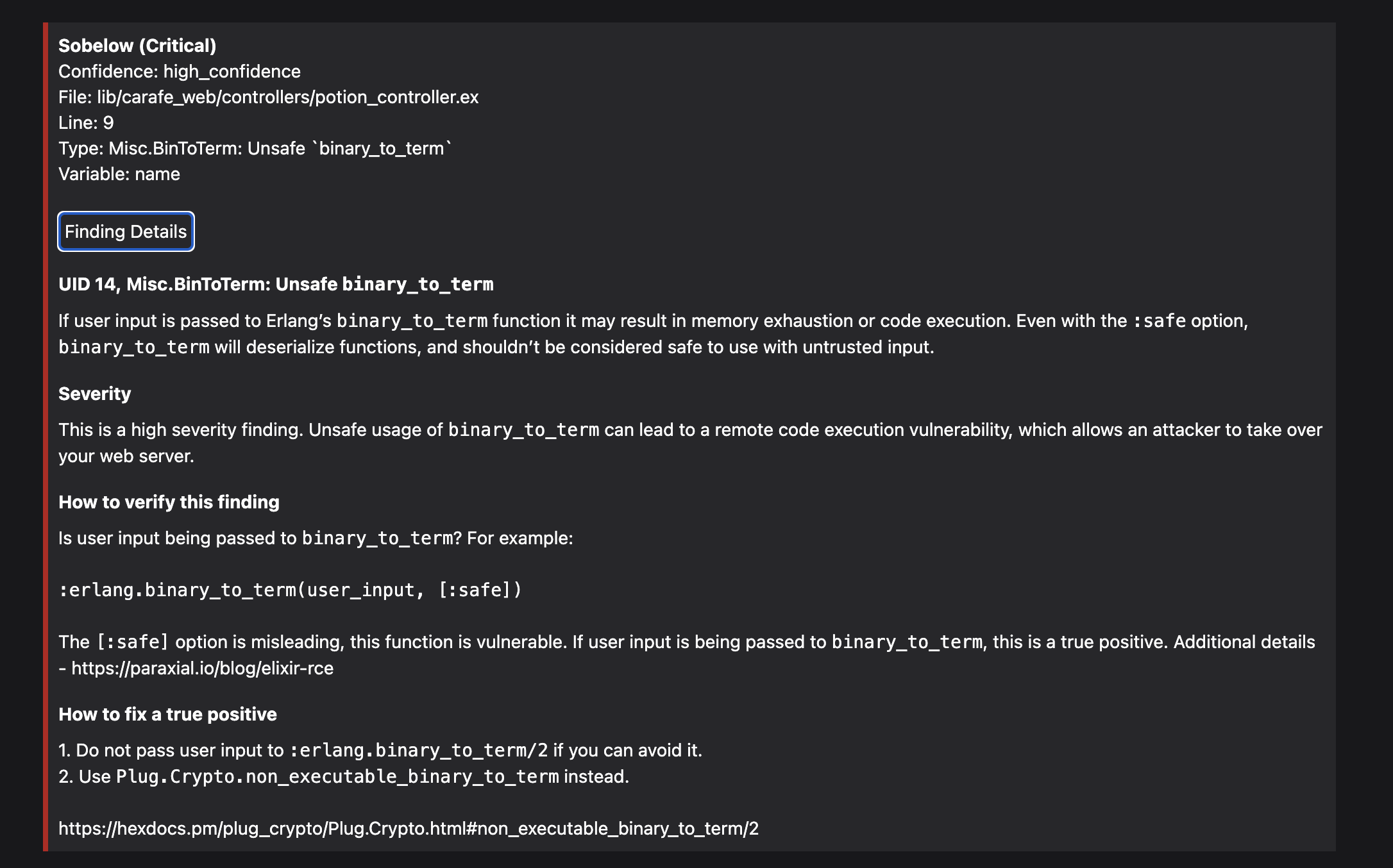
Vulnerability Triage
A common barrier to using security tools in Elixir is the high number of initial findings. Paraxial.io is able to prioritize findings by severity, meaning your limited time is allocated to fixing the most severe problems first.
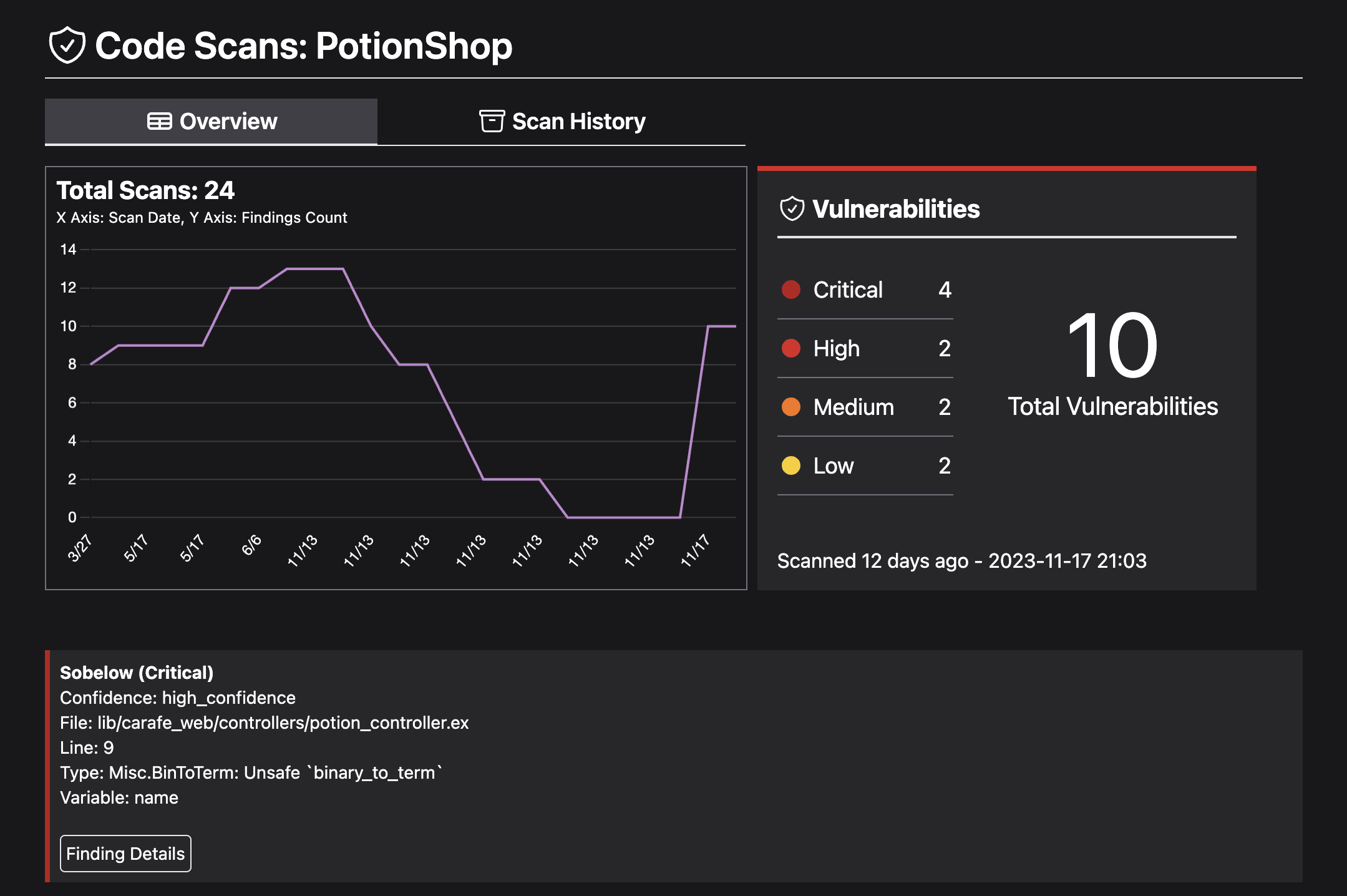
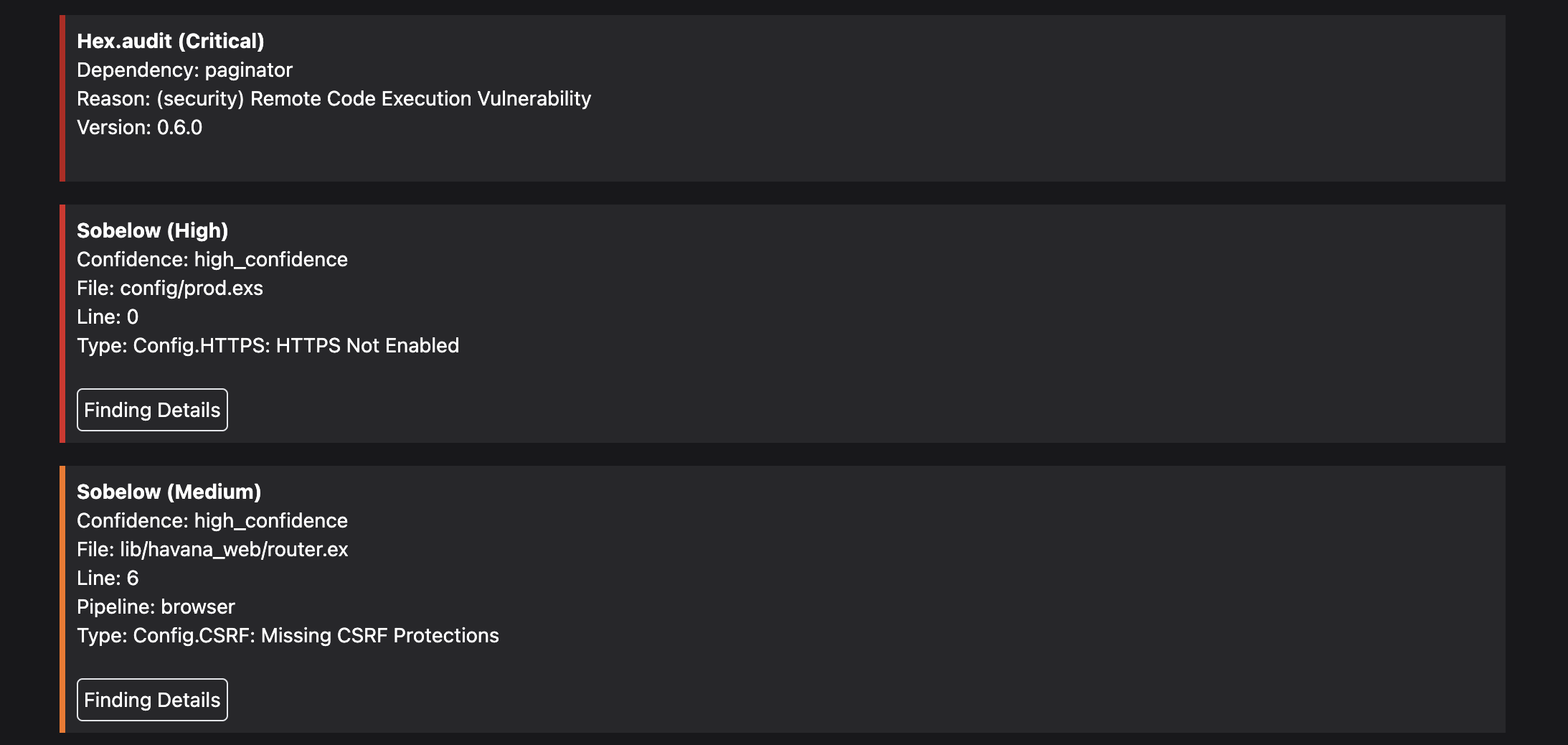
Paraxial.io also provides detailed information on each Sobelow finding, helping developers confirm and fix true positives.
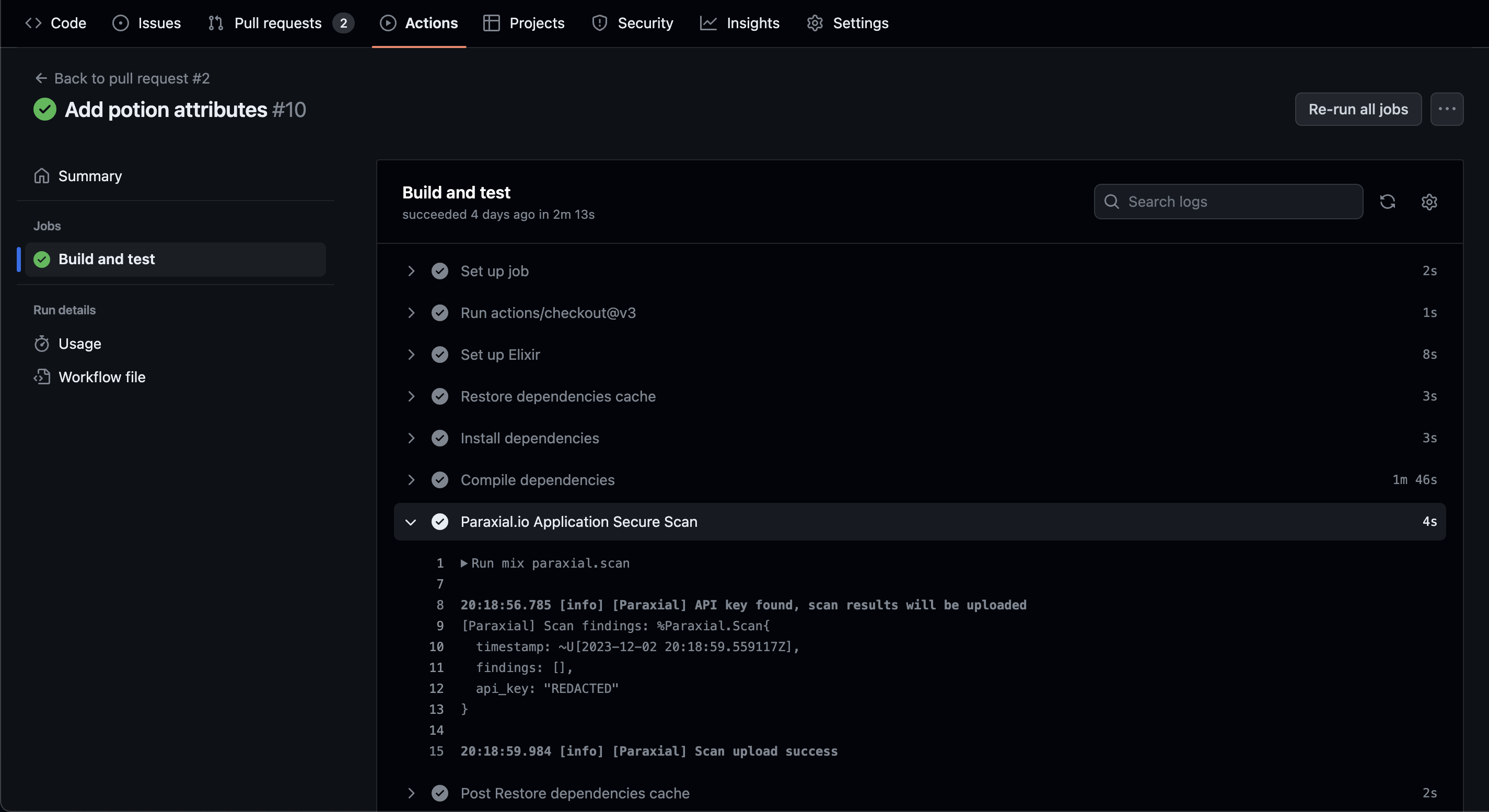
Automated Security
The Paraxial.io mix task is fully compatible with your CI/CD pipeline, because it runs as normal Elixir code. For example, you can configure a Github action to check each new pull request for security problems.
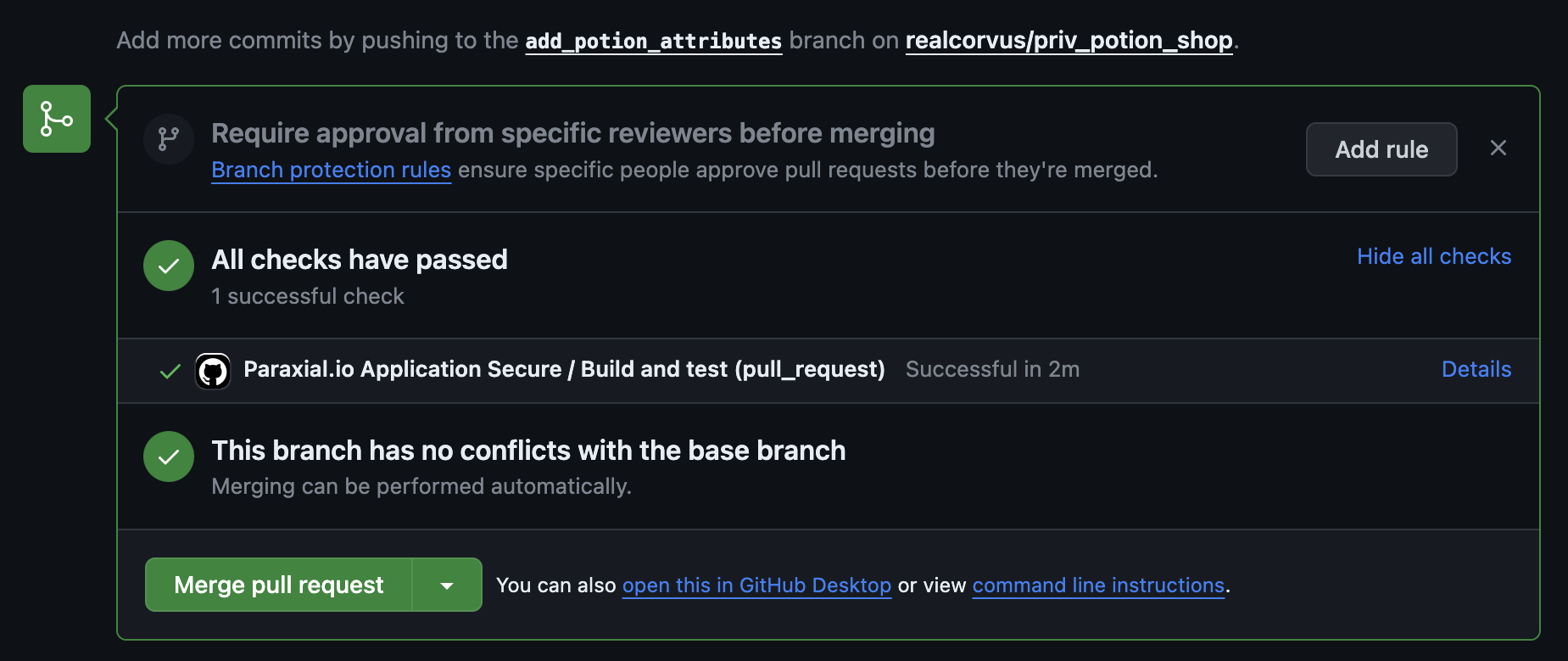
Paraxial.io scans your entire project in just a few seconds. If no issues are found the build is successful.
Security Roadmap
This release of Paraxial.io is designed to help you secure your Elixir application. To understand the reason these features exist, the document Elixir Security Roadmap: A CTO Level Guide goes into detail on this topic. Paraxial.io helps you achieve the following milestones:
- Asset Management and Updates
- Developer Education
- Elixir Code Security Tools
- DDoS and Bot Attacks
- Logging and Monitoring
There is a massive amount of generic cyber security guidelines, frameworks, and advice available today. The topics selected in this report are the most relevant for companies using Elixir.
Paraxial.io stops data breaches by helping developers ship secure applications. Get a demo or start for free.